Talking about the vast universe of keys might come across as uninspiring or fascinating, however, it harbors a rich variety of amazing technologies, mechanisms and solutions, some of them simple, others incredibly advanced. Each key hides a secret within it, and in this article we aim to reveal some of them. We begin by examining the key components, which essentially fall into two parts: handle and blade.

The components of a key
The handle can take various shapes and can be made from a wide range of materials, depending on the customer’s preference: the standard is to use nickel-plated brass, but it can also be made from plastic. Of course, the handle can come in a variety of shapes, including the classic round or square model, but it can also be ergonomically designed, handle-like or handle-like, and it can be fixed or collapsible to reduce protrusion in places of great passage. Finally, you can customize the handle with the customer’s logo or OMR logo to give your key a personalized touch.
The blade or barrel is the part that houses the lock release code and can take several configurations, including:
- Ciphered: this is the most common and widespread type of key, the classic key that has an indentation along one or both edges.
- Imprinted: there is a concave, geometric shape at the end of the blade, such as a triangle or square.
- Pin tumbler: relies on “metal pins” of different lengths arranged radially for encryption.
- Tubular: the blade is cylindrical or tubular in shape
- Wave with side track: new key coming for 2024.
We explore in detail how the various unlocking methods used in locks work and analyze the complex mechanisms behind common objects such as keys. We will delve into the analysis by following a path from basic protections to those of increasing complexity. In doing so, we will gain a deeper understanding of how locks can be opened and the challenges security systems face in effectively protecting access and resources.
Socket key
This type of key is commonly used in low-risk technical compartments, such as control panel doors and water and gas meters.
Compared to its encrypted counterpart, it offers a lower level of security and is often used in contexts where it is a priority to allow access to technical operators rather than to prevent unauthorized ones. For example, anyone with a socket key with a T5 triangular shape can open your water meter door, but this design allows authorized operators to access hundreds of compartments with a single key, simplifying inspection and maintenance operations. At the same time, a closed door provides basic protection for the tools in the compartment, and unauthorized access is restricted and discouraged.


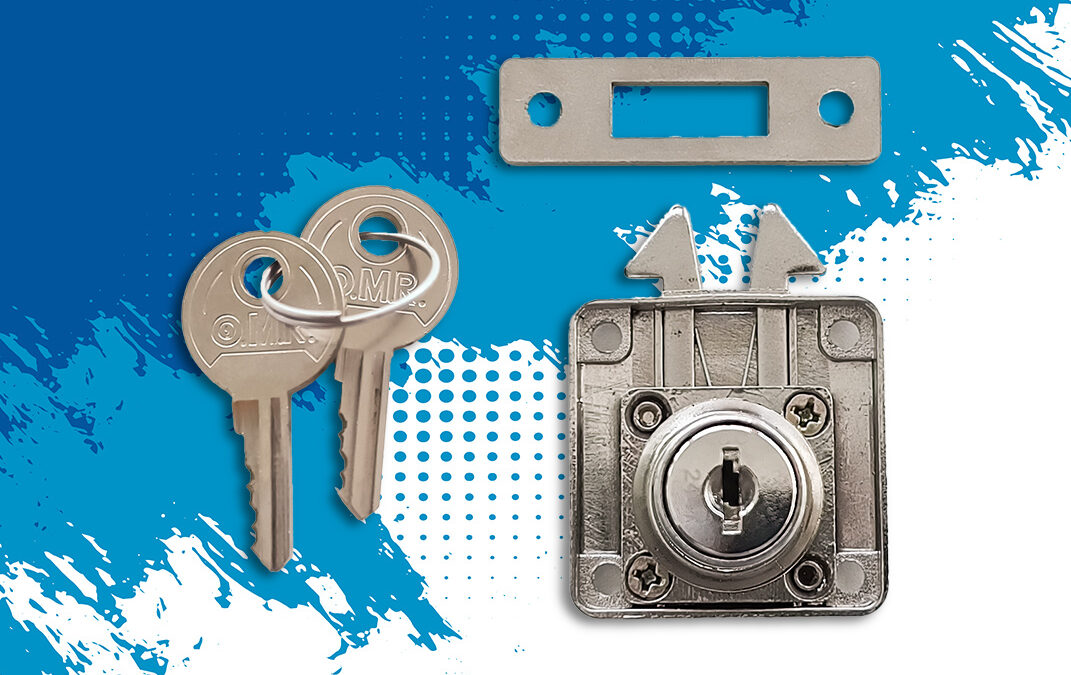
Flat key
This type of key finds application in a wide range of situations, such as lockers, chests of drawers, ski racks, luggage racks, mailboxes, filing cabinets, and many more.
Characterized by a high level of protection, there are two main variants: symmetrical and non-symmetrical. In the first case, the key is reversible and can be inserted into the lock patch in either direction, while in the non-symmetric variant there is only one way of inserting the key. The flat key blade has a code printed at the root of the blade, which identifies the key model. This code is not to be confused with the encryption code, which is secret and determines the operation of the key. The notched part of the key corresponds to a numerical code, such as “124123.” The depth of the notches determines the corresponding number; a “one” notch will be much shallower than a “seven” notch.
In addition, the blade is usually traversed lengthwise by two rails, one on each side, which help keep the key in the correct position during insertion and rotation in the lock. This complex design provides a high degree of security, effectively protecting against unauthorized access.
Pin tumbler wrench
This particular type of key is used in applications that require a high level of security, such as vending machines, machinery and elevator actuator panels, security boxes, parking meters, coin changers, and the like.
The pin tumbler key is distinguished by its unique structure designed to provide advanced protection. It consists of a circular bushing within which are arranged in a radial configuration six metal pins of different lengths, each representing a digit of the six-digit code. For example, the length of the pin representing the digit “one” will be shorter than the length of the pin representing “four.”
The circular metal part along the edge of the key is used to keep the key aligned during insertion and rotation in the lock. It is necessary to push the key toward the lock, thus allowing the pins to press against their respective pins inside the lock. This action unlocks the mechanism and ensures that the desired access is opened. The pin tumbler key is a sophisticated solution for access protection in environments where security is paramount.


Tubular wrench
This type of key is used in a variety of contexts, protecting turnstiles, glove compartments, elevator and machinery control panels, vending machines, and others.
The operation of a tubular key has affinities with that of pin tumbler keys, but with one significant distinction: the pins are not located on the key itself, but rather inside the lock. On the tubular key, we find seven concave incisions of different lengths. To open the lock, it is necessary to press the key all the way in and allow the internal pins to align according to the correct combination. Only then will it be possible to turn the lock and gain the desired access.
The tubular key therefore is keyed different, and it is possible to make it keyed alike or unique. In addition, the locking pins are neither directly visible nor accessible from the outside, further helping to raise the level of protection offered by this type of key.
Key encryption: unique, keyed alike or passe-partout?
Are all keys the same? Not really! In the world of industrial key manufacturing, there are different levels of complexity related to encryption. Some applications do not require a variation of ciphers, take for example locks for balcony cabinets or lockable valves: in these cases, it is possible to manufacture a large number of keys that are virtually identical, and in this case we speak of “keyed alike.” Of course, this is not always the case, and OMR can handle different ciphers to meet specific customer needs. This approach is referred to as “mixed encryption,” since the keys can actually all be unique.
There is also a further level of complexity involving keyed different encryption with the added concept of passe-partout. In other words, it involves a set of keys that are all different, flanked by a group of special keys capable of opening all the different combinations. This scenario applies, for example, to cabinets and drawers in offices: each employee is responsible for the own archive, but management can have access to all cabinets through the use of the passe-partout key.
OMR Key Production Process
As is the case with all OMR-branded products, key production is handled in-house by qualified personnel. Our team takes care of every step of the process, from the handling of the raw material that arrives at our plants to the shipping of the final product to the customer.
Each type of key follows a dedicated and focused manufacturing process. Some keys go through automated mass production processes, as is the case with pin tumbler keys, while others, such as pin tumbler keys, are handcrafted and manually assembled. In this way, we ensure the highest attention to detail and precision in the production of keys that meet the highest standards of quality and security.

We would like to conclude our journey into the world of keys by paying special tribute to the Michel key, a historical artifact of the 1950s industry, which is a fundamental part of OMR’s history and testifies to the beginning of the entrepreneurial adventure of Mario and Roberto Olivi, who started from a small workshop in Piedmont.
The Michel key is a symbol of OMR’s past and its roots. Through the hard work and dedication of generations, the company has grown to what it is today: a manufacturer of high-quality products, entirely made in Italy, distributed throughout Europe. As we look back on those early days, we see the long road we have traveled together with you, and we enthusiastically prepare for the future.
P.S. Speaking of the future, it is legitimate to wonder whether one day keys will be completely replaced by electronic access systems based on NFC, RFID and Bluetooth. And what will happen in the event of battery failure or power outages? This is a fascinating topic that OMR has been thinking about for some time, offering cutting-edge, sustainable and secure solutions. For more insights, we invite you to read articles on Hellock, the electronic key or numeric combination lock.








0 Comments